kusabi

kusabi is electronic certification services with a new concept utilized blockchain technology. It is a "Security Electronic Certification Infrastructure Services" that provides a Digital ID (Certificate Key) has Confidentiality, Integrity, Availability, and Authenticity in logical. Also, it freed from the expiration date limit of the original digital certification.
Overview
Many technologies have already permeated our lives, and people's lives are becoming more convenient in every way. Our lives have been enriched, and we have entered an era in which AI derives optimal solutions by aggregating and analyzing information automatically on various IoT devices such as security cameras, water・electricity measuring instruments, temperature・hygrometers, and a system triggered by information on non-contact devices using IC chips. In addition, as various devices become IoT in the future, changes will accelerate to a society that cannot be imagined by common sense and stereotypes.
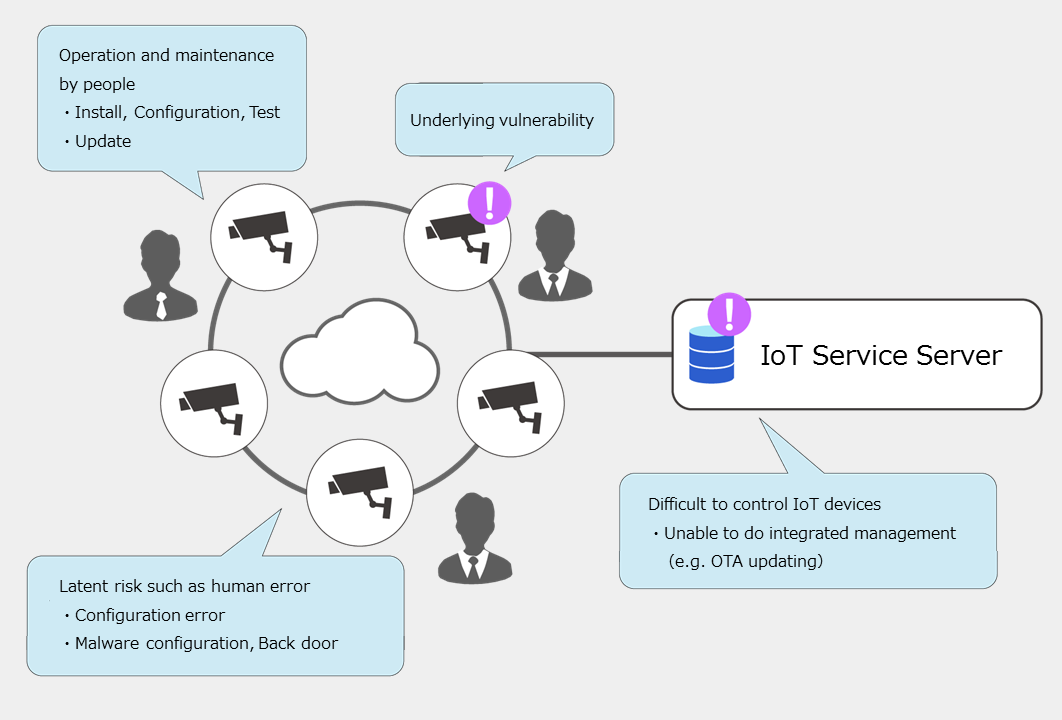
Under such circumstances, if a security camera is illegally accessed, it immediately changes from safe to risk. There are always security risks behind convenience and affluence, such as when the position or status of a device is illegally acquired・・・, or when it is rewritten to an incorrect value・・・.
However, many devices that handle information have their resources optimized for their original purpose and function. So it is difficult to apply existing security measures. As the number of IoT devices whose information is always online increases in the future, the risk of operational limits being reached by existing management and leaving vulnerabilities unconscious of their existence will increase. Not only will various security issues and maintenance issues increase, but secondary damage such as human error will also increase, and there will be a lot of issues to be improved.
The kusabi is a Security Electronic Certification Infrastructure Services with a new concept by system monitoring pioneer IBC developed utilizing software technology to make it easier to incorporate electronic certifications useful for security measures for IoT security issues and to focus on business promotion and development work.
We have prepared a white paper that explains the details of kusabi in simply.
Anyone can view this white paper free by requesting the following.
We hope that you will take this opportunity to read it and help solve IoT security issues.
■White paper request
If you want the kusabi white paper, please apply to this email address.
The title should be "White paper request" and the text should include "company name", "department / position", "name", "phone number", and "email address".
(We may refuse the requests from our competitors.)
E-mail:kusabi-info@ibc21.co.jp
Concept
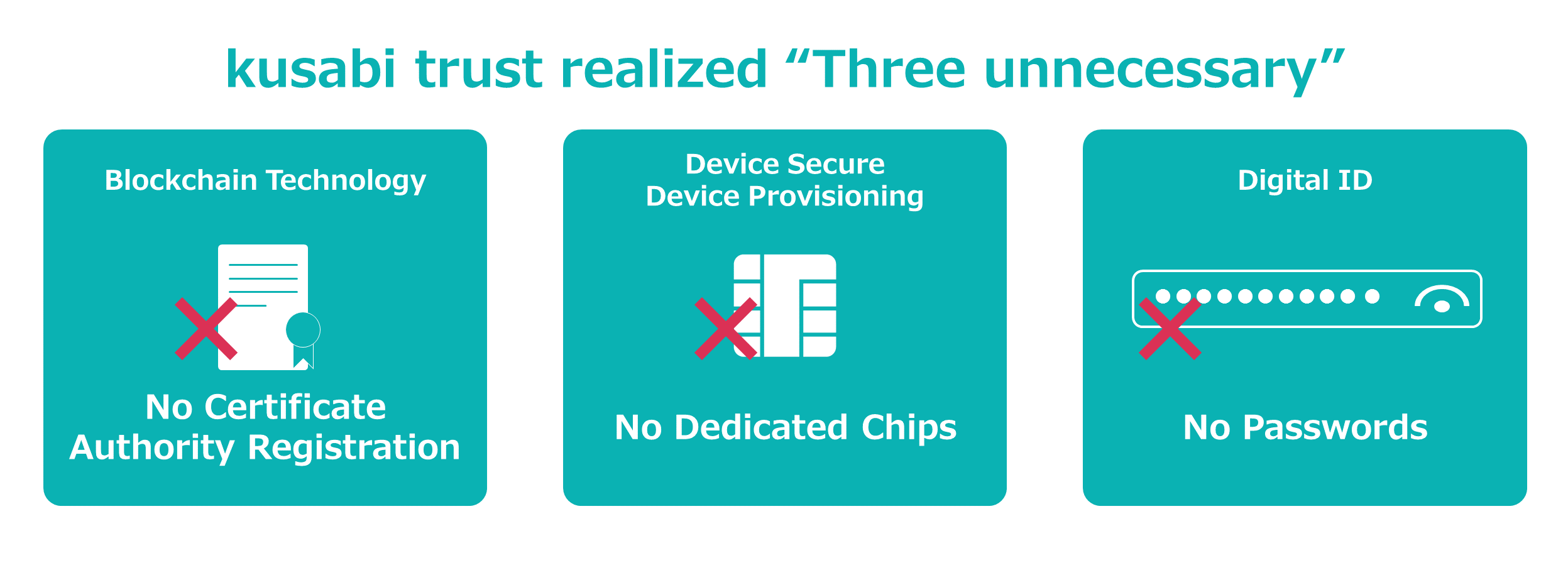
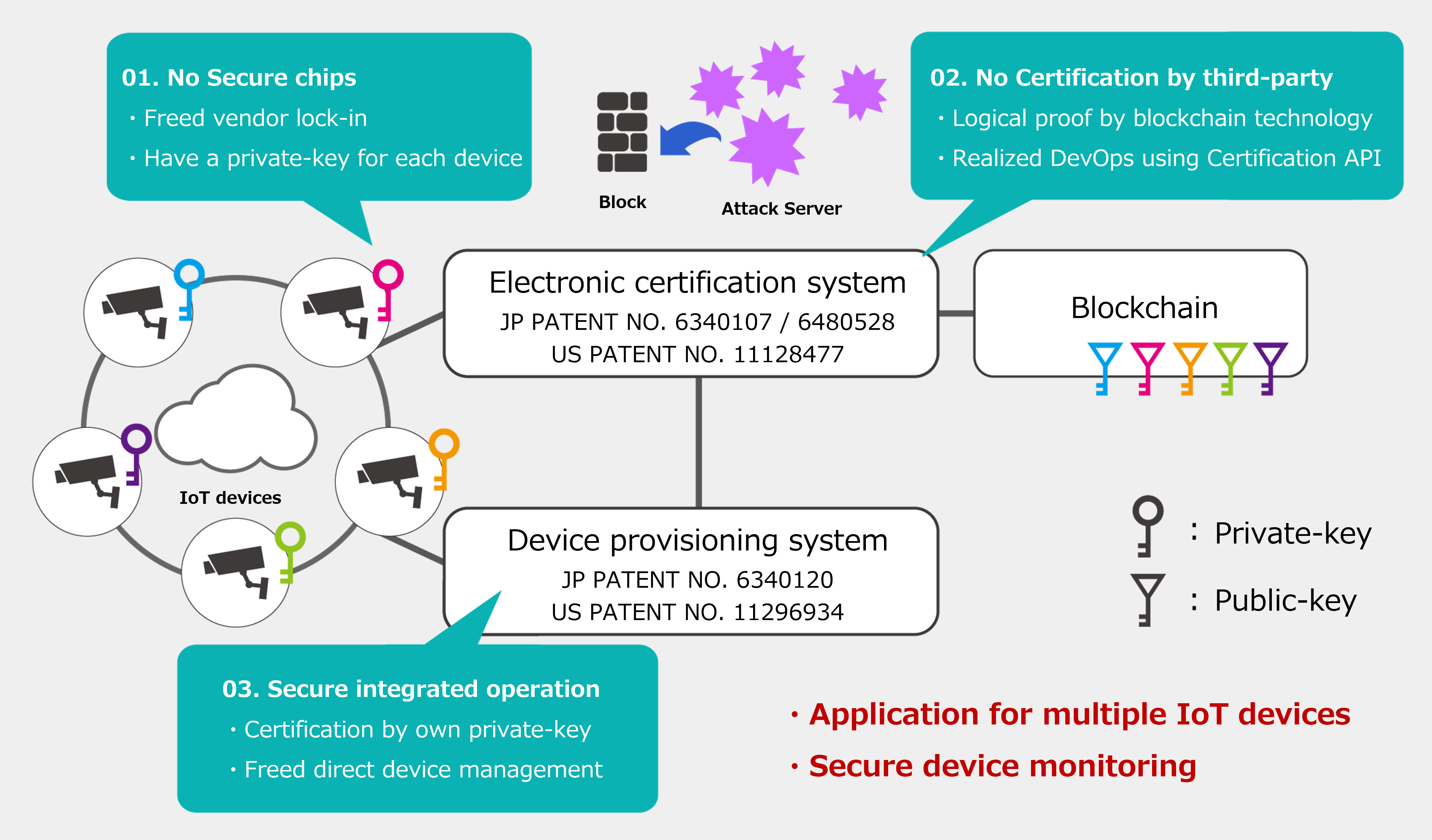
◆No Certificate Authority registration
The kusabi provides services that efficiently utilize public key cryptography. By utilizing the logical characteristics of blockchain technology, and managing the process at the CA (Certificate Authority), we can compatible the simplicity of private authentication and credit equivalent to the CA(Certificate Authority). It is also possible to issue in bulk at any time you want, and contributes to efficiency by eliminating various intermediate costs. Furthermore, with kusabi, it is possible to realize DevOps with security by managing the registered public key with electronic certification and distributing the public key only at the request of the required system.◆No Dedicated Chips
Some devices such as IoT have performance restrictions, and in some case credit is secured by enclosing a certification with a dedicated chip, but in other cases it is difficult to implement a dedicated chip. The kusabi takes advantage of its key characteristics to provide strong device security with software. Depending on the configuration, it is possible to control without enclosing the private key on the terminal side.◆No Passwords
Most cyber attacks are triggered by login steps such as WEB management screens, TELNET, and SSH, and disclosure of device-specific standard account information (root, admin, etc.) creates a situation where brute force attacks are likely to occur. In addition, it may be attacked to vulnerabilities from public ports for operation.The kusabi uses the issued Certificate Key (Digital ID) to prevent access to the local account and password from the public port, reducing the risk of external attacks and password leakage, and unmanned operating on the terminal side.
Business solution by kusabi model
01. Current Status of Security
Many of the current IoT security measures follow the existing PC security measures (ID, Password).However, existing security measures are often inconvenient because devices are the predominant in IoT business use cases. Complete control is impossible to the potential risks such as simple human error, easy password setting (initial setting / reuse), and malicious preparation (backdoor / retiree, etc.).
In the future, the diversity of IoT devices will become a main issue in security measures. PC and other devices are based on a standard OS, and a mechanism for distributing vaccine software as a countermeasure against malware attacks was effective.
However, it is difficult to take countermeasures in IoT which is premised on diversity, because the vaccine itself is difficult to divert. As a business use case for IoT devices, it is also an issue to install them in large numbers in various locations.
Controlling a huge number of devices is a risk factor, and operating costs are increasing. The out of control devices will destroy the social infrastructure.
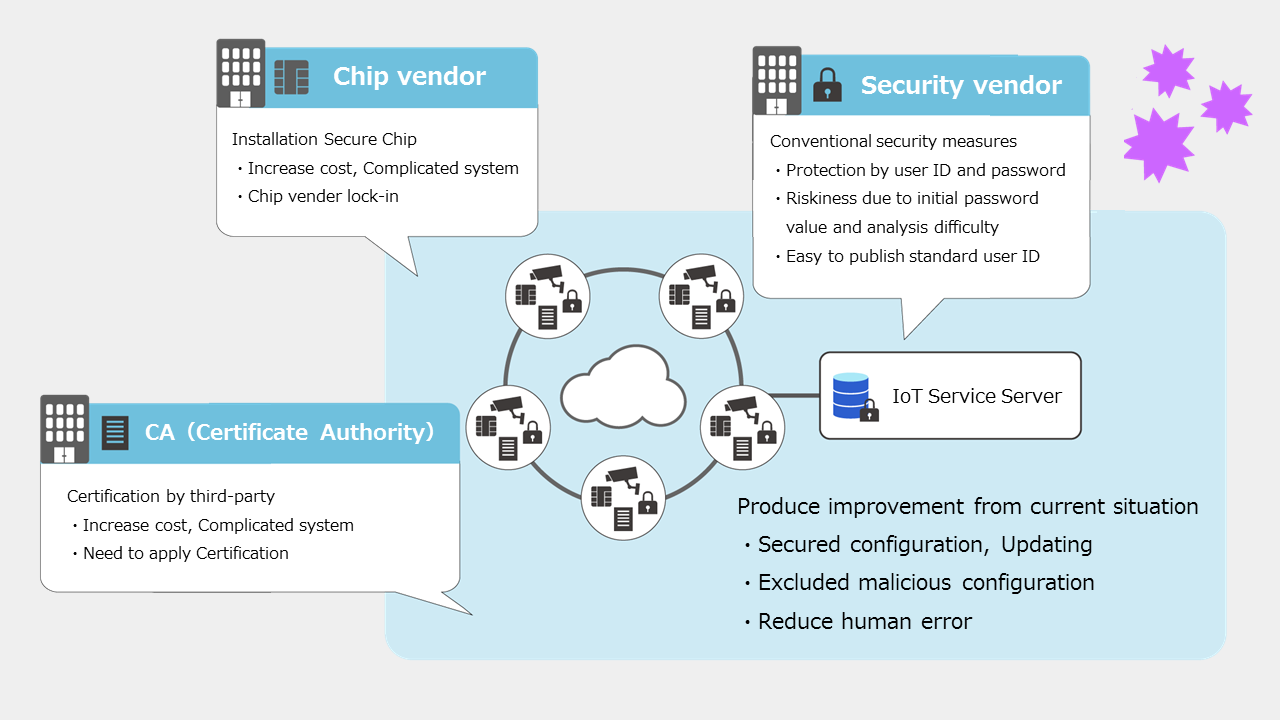
02. Improvement and new problem by a dedicated chip + CA(Certification Authority) model
A security model using dedicated chip and CA (certificate authority) is drawing attention as an increasingly serious IoT security measure. Although it is an effective measure for security, it is necessary to consider investment in manufacturing cost and operating cost when embedding physical devices and linking with CA (Certificate Authority). Increasing vender dependence on dedicated chips will increase issues and consideration in product development for highly functional IoT devices. Furthermore, it will be expected that traffic failures will occur due to the concentration of inquiries from many devices to the CA (Certificate Authority).The dedicated chip + CA (Certificate Authority) model evoke the following new issues.
03. Business solution by kusabi model
The kusabi model realizes IoT security by using the key of new idea by original device provisioning technology, and electronic certification by blockchain technology. Security measures by utilizing electronic certification keys with blockchain, API, and PKI enable flexible response to device evolution and cost reduction. In addition, because it is realized by software, it can be applied to various environments and used for devices, and new technologies can be easily incorporated.In other words, the kusabi model can be said to be a "Security Electronic Certification Infrastructure Services" that can provide keys applied not only to IoT but also to various business use cases.
Comparison summary of kusabi model and hardware + CA model
The kusabi Model | The Dedicated Chip Model | ||
| Player | Chip vendor | 【unnecessary】 Utilized the electronic certification system of kusabi | 【necessary】 Write the key to the hardware module of the dedicated chip at the production step. |
| CA (Certification Authority) | 【unnecessary】 Utilized the electronic certification system of kusabi | 【necessary】 Issuing and managing the electronic certificates on each device at the shipping step using the key of the above hardware module. | |
| IoT device vendor | 【necessary】 Install the startup / initialization program using API of the kusabi device provisioning system | 【necessary】 Install the startup / initialization program using PKI Library of CA. | |
| Integrator | 【necessary】 Provide an edge server using API of the kusabi device provisioning system | 【option】 Presence as an orchestrator of chip vendors, CA and security vendors. | |
| Cost | License fee of kusabi | License fee is accrued for each player of chip vendors, CA and security vendors | |
| Versatility | A system customized for each user can be provided by an integrator. | It is locked in to the system (service) provided by each player of chip vendors, CA and security vendors. | |
kusabi API Terms of Use
By using the kusabi API, you agreed to the terms herein.
kusabi API Terms of Use(Japanese)
CONTACT
お気軽にお問い合わせ下さい
03-5117-2780